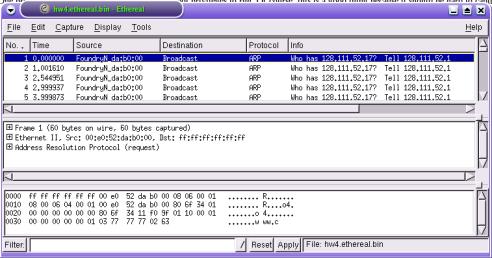
Figure 1. Ethereal snapshot
The goal of this assignment (and the next assignment, HW#4) is to help you understand what is going on in the network by focusing on exactly what bits, packets, and information flows across a network link. This task is rather difficult because network protocol designers have worked hard to provide significant abstraction to the higher layer applications. Therefore, as a user at the highest layer of the protocol stack, you are able to see very little of what happens in the network. Never fear though, there are tools that we can use. HW#3 and HW#4 are different than in previous years. Instead of analyzing all parts of the traffic in one larger assignment, the work is being divided into two assignments. The focus of HW#3 is on the Network layer and below while HW#4 focuses on the Transport and Application layers. While you will still need some idea of what is happening at the transport and application layers for HW#3, it will not be the emphasis.
The goal of this assignment is to examine real protocols in use and understand the communication that takes place in a network by examining the bits that flow across a network hop. For this assignment, you should focus on the lower level protocols, i.e. pay more attention to the DLL/MAC layer and the Network layer.
For HW#3 and HW#4 you will use the application ethereal. Ethereal lets the user capture packets from the network and save them for viewing at a later time. When running Ethereal you should see something like Figure 1. Ethereal is available for most platforms, including Windows, from http://www.ethereal.com/. It is also available in the CSIL lab either in KDE under "Internet", or by simply typing ethereal at the command line.
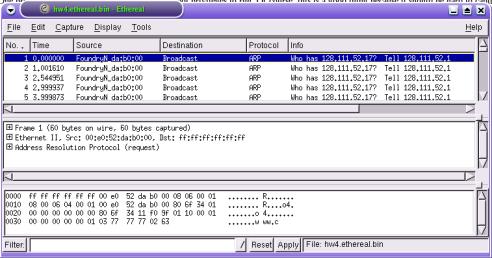
Figure 1. Ethereal snapshot
One problem though: ethereal usually requires "root privilege" to run. Of course, this is a good thing because it should be hard to capture packets on the network! So, the capturing has been done for you, and a capture file has been created. Take the network-traffic.bin file (NOTE: Make sure you download this file, i.e. right click and select "Save Link As".) and use it as the source file for ethereal (HINT: do a man ethereal and look at how to use the -r option.). While you cannot run ethereal to snoop packets off the network in real-time without root access, you can run ethereal on a file. Part of doing this assignment well is learning how to effectively use ethereal, so you will likely want to read and/or reference the User's Guide. You will also want to use the GUI in ethereal to more closely investigate what is happening in this trace. Some of the things going on in the trace will contain protocols we have not gone over in class. You will have to use one of the class textbooks or Google as references to find information about these protocols. Finally, parts of the TA discussion section will be reserved for asking questions about this assignment. So be prepared to ask questions when the time comes.
A significant portion of the grade for this assignment will be based on your ability to communicate that you understand everything about the packet trace. This implies, as usual, a clear, concise write-up! To help get you started, below is a set of sample questions that you will want to answer about the packet trace. However, these questions only serve as examples of the kinds of things that are important. They serve as a starting point and are not exhaustive. Furthermore, the questions are not organized in any sort of easy-to-follow way (like your write-up should be). They are only provided as a guide to help you find the most interesting aspects of the trace. In this assignment, you do not need describe anything about the Transport or Application layers.
So, how should you proceed? Start by considering the following questions:
The format for your write-up will essentially follow the same guidelines as HW#1 (a single DOC or PDF file). Within the document though, you are free to organize information about the packet trace in any way you like. One suggestion is to be creative (but do not assume that creativity can be used as a substitute for technical thoroughness). Before even starting your write-up, you should first answer the questions above and understand what is going on in the trace. When it comes to the write-up, you likely will not want to include the list of questions with answers, but knowing the answers is a critical first step before you can think much about how to organize your report. In addition to the individual questions, you will also want to pay attention to some high level questions: What happened in the trace? What does the network topology look like (and what nodes/devices have what addresses)? Who sent traffic and to whom? Who responded?
As a high-level goal, try to present the trace in a way that provides multiple levels of abstraction. For example, first describe the session, then describe the flows, then describe the packets in a flow. Then maybe describe anything unusual in the trace.
Organizing the large amount of information in the trace into a clear and coherent format will be one of the harder parts of the assignment. Because there is so much hard-to-organize information, you will have to make some hard decisions and use some creative solutions to clearly convey to a reader what is happening.
As a final hint, there are some good examples of how to write this kind of report on the Internet.